Currently writing a micro service for the discussion related to:
Python Code for some context - if you want to run this you need to replace some variables:
def createUser(assetID, password):
rURL = f'{apiurl}/api/master/user/master/users'
rHeaders = {'Authorization': f'Bearer {thismodule.apitoken}'}
rData = {'enabled':True,'secret': f'{password}', 'realm':'master','roles':[],'previousRoles':[],'realmRoles':[],'previousRealmRoles':[],'userAssetLinks':[{'id':{'realm':'master','assetId':f'{assetID}'}}],'serviceAccount':True,'username':f'{assetID}'}
r = requests.post(url=rURL, json=rData, headers=rHeaders)
return r.status_code, json.loads(r.content)['id']
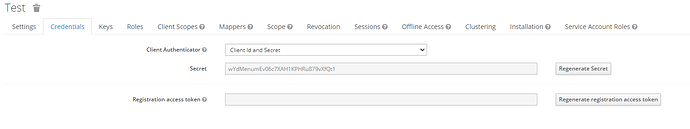
The 'secret': f'{password}' is being ignored even tho the swagger states this body:
{
"realm": "string",
"realmId": "string",
"id": "string",
"firstName": "string",
"lastName": "string",
"email": "string",
"enabled": true,
"createdOn": "2023-06-14T17:28:35.288Z",
"secret": "string",
"attributes": {
"additionalProp1": [
"string"
],
"additionalProp2": [
"string"
],
"additionalProp3": [
"string"
]
},
"serviceAccount": true,
"username": "string"
}
What “string” for secret is needed to be accepted?
Ignore the part where I use the assetID as username ![]()
I also copied this body from the network inspect when creating a User and linking it to an asset.
Yes I know you need to also POST f'{apiurl}/api/master/asset/user/link'